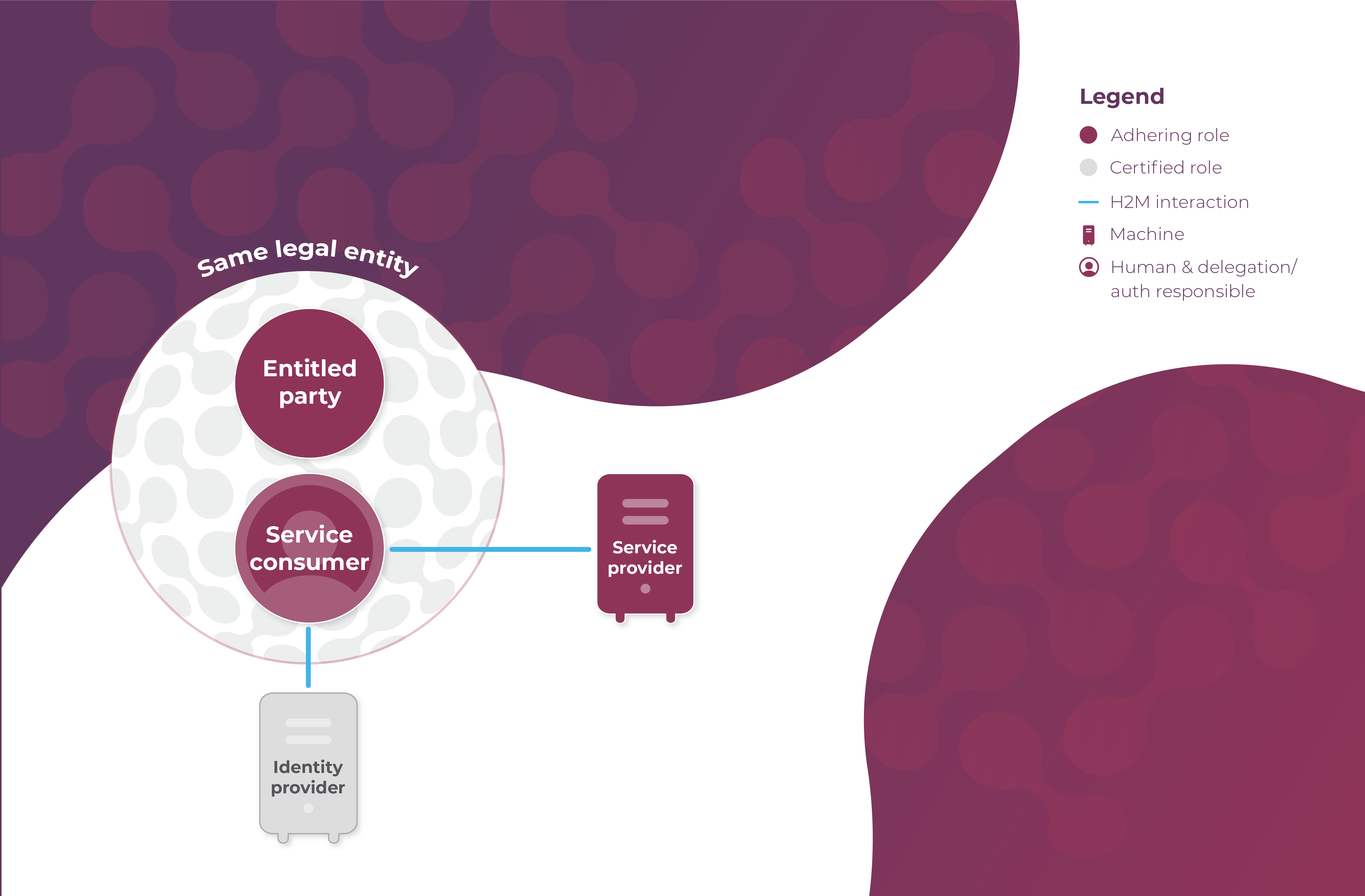
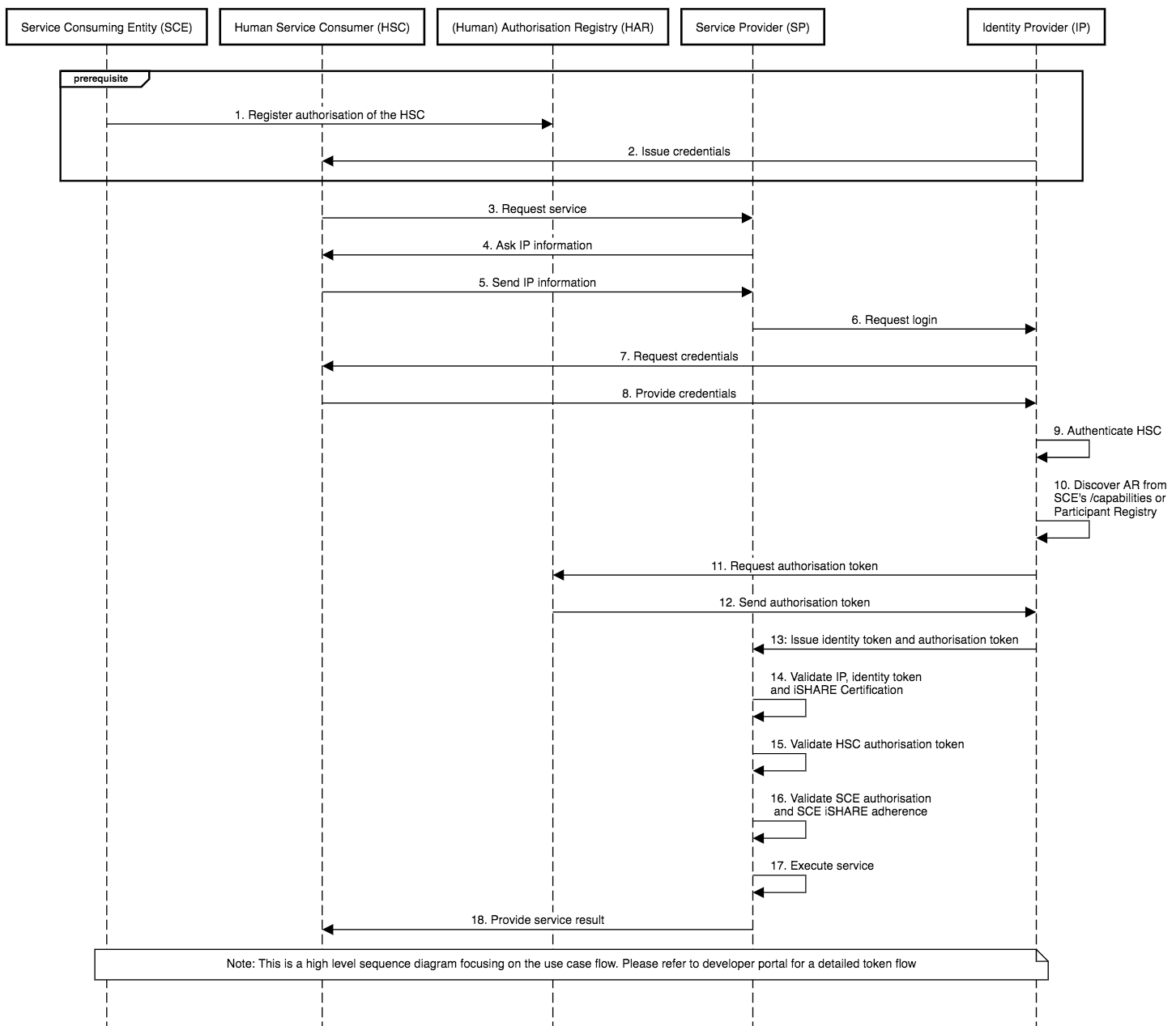
Authorisation via Identity Provider Checking Authorisation Registry (AR)
.png?alt=media)
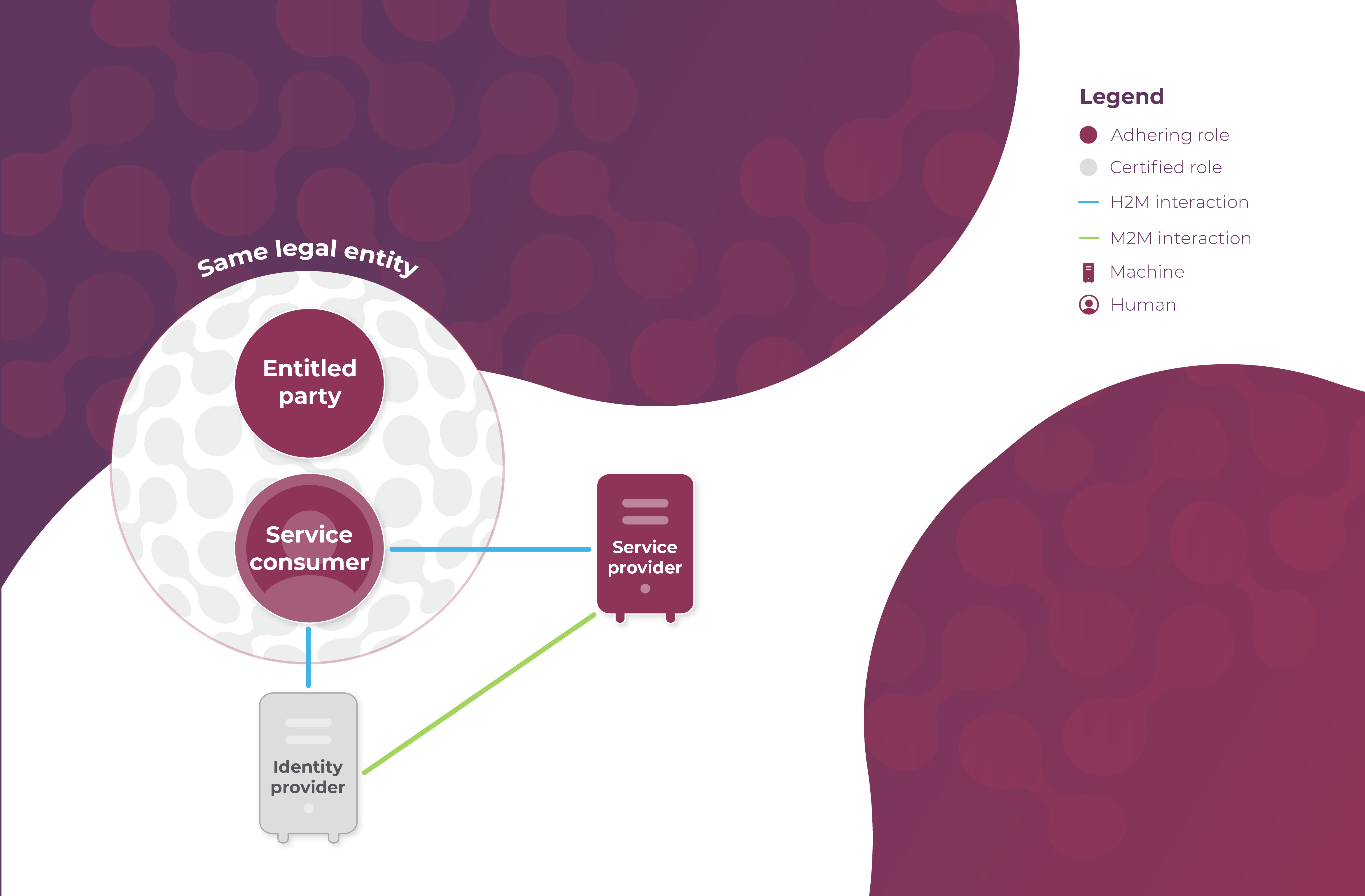
Authorisation via Identity Provider Providing ID of Authorisation Registry to the Service Provider
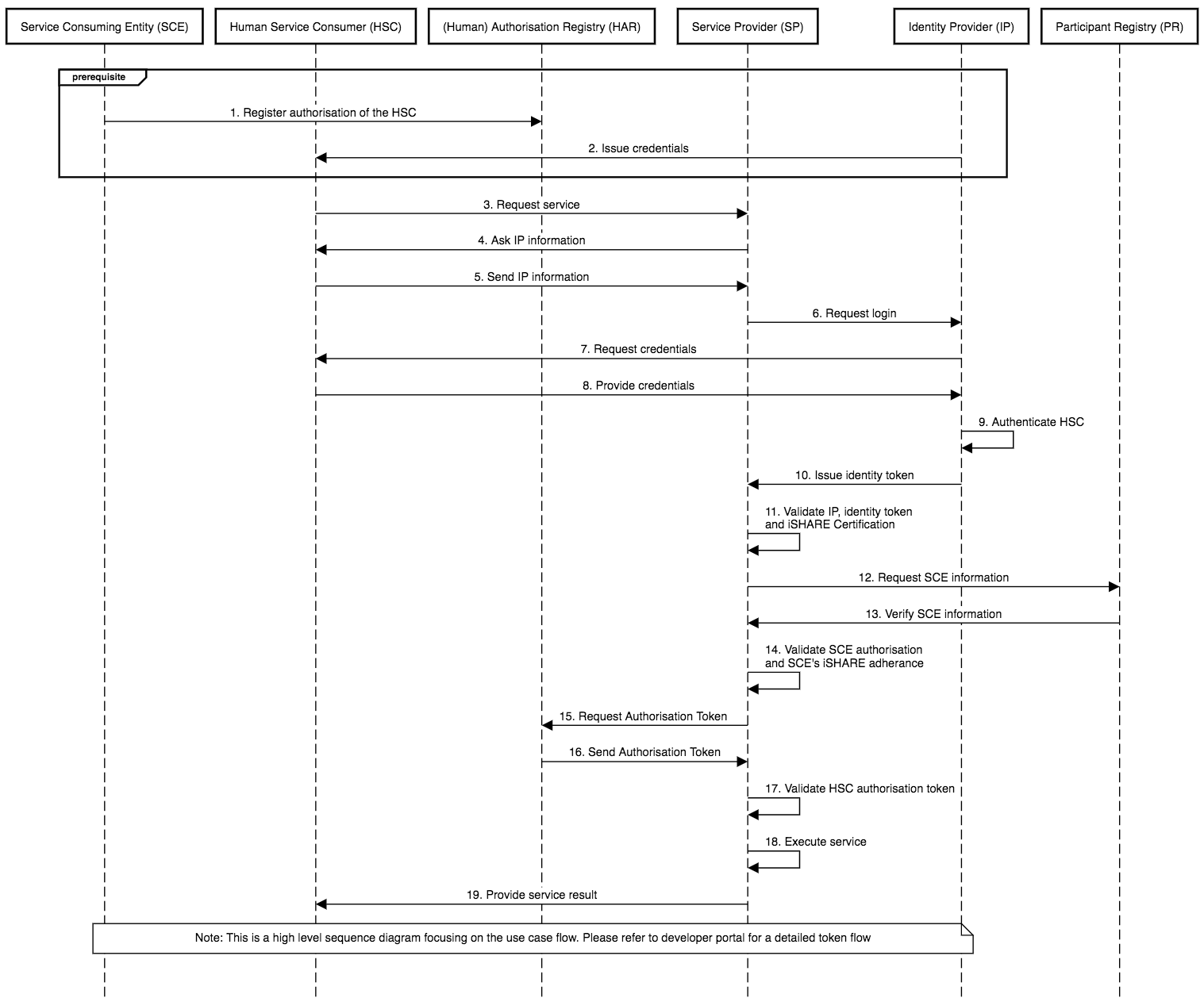
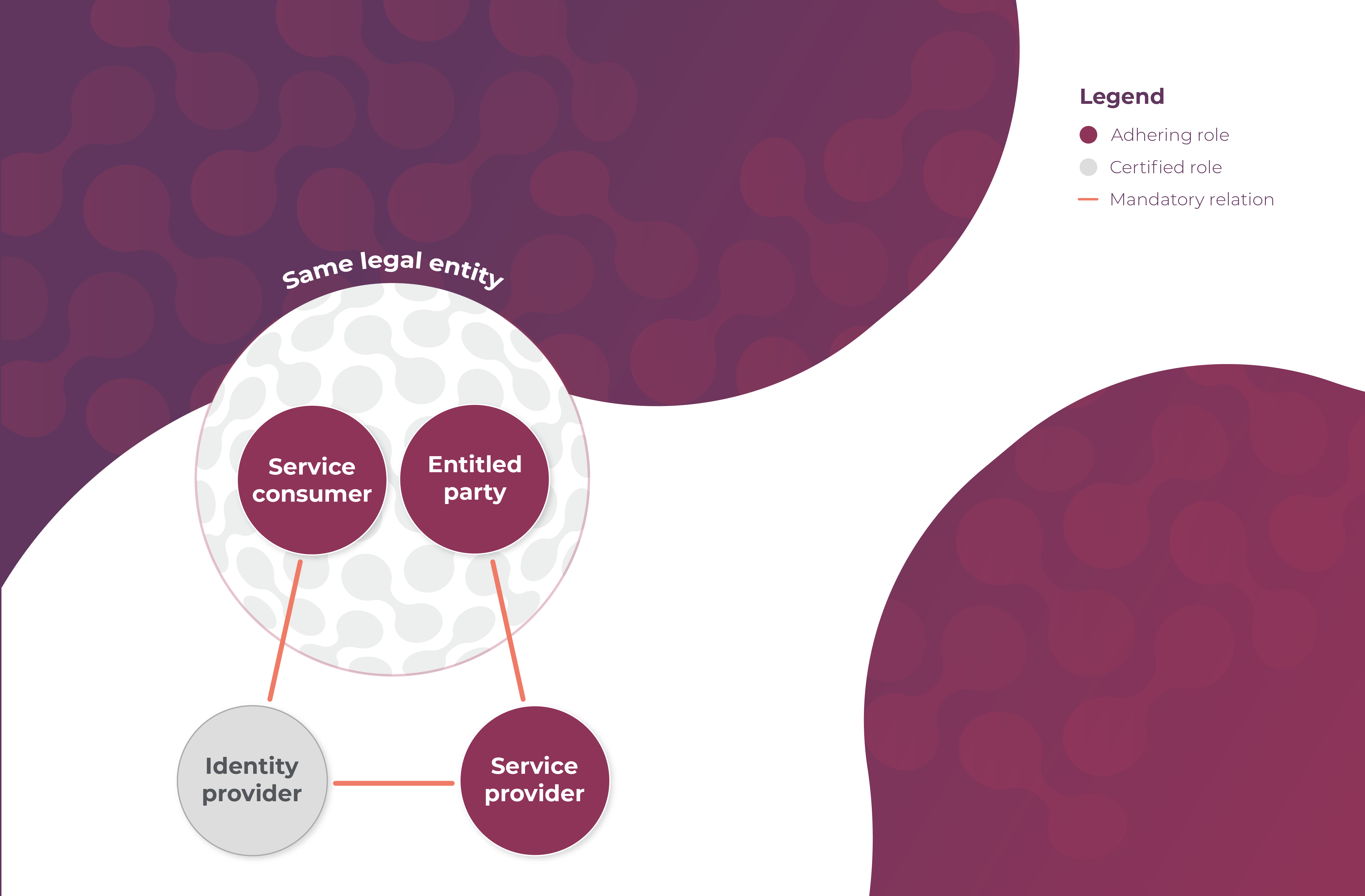
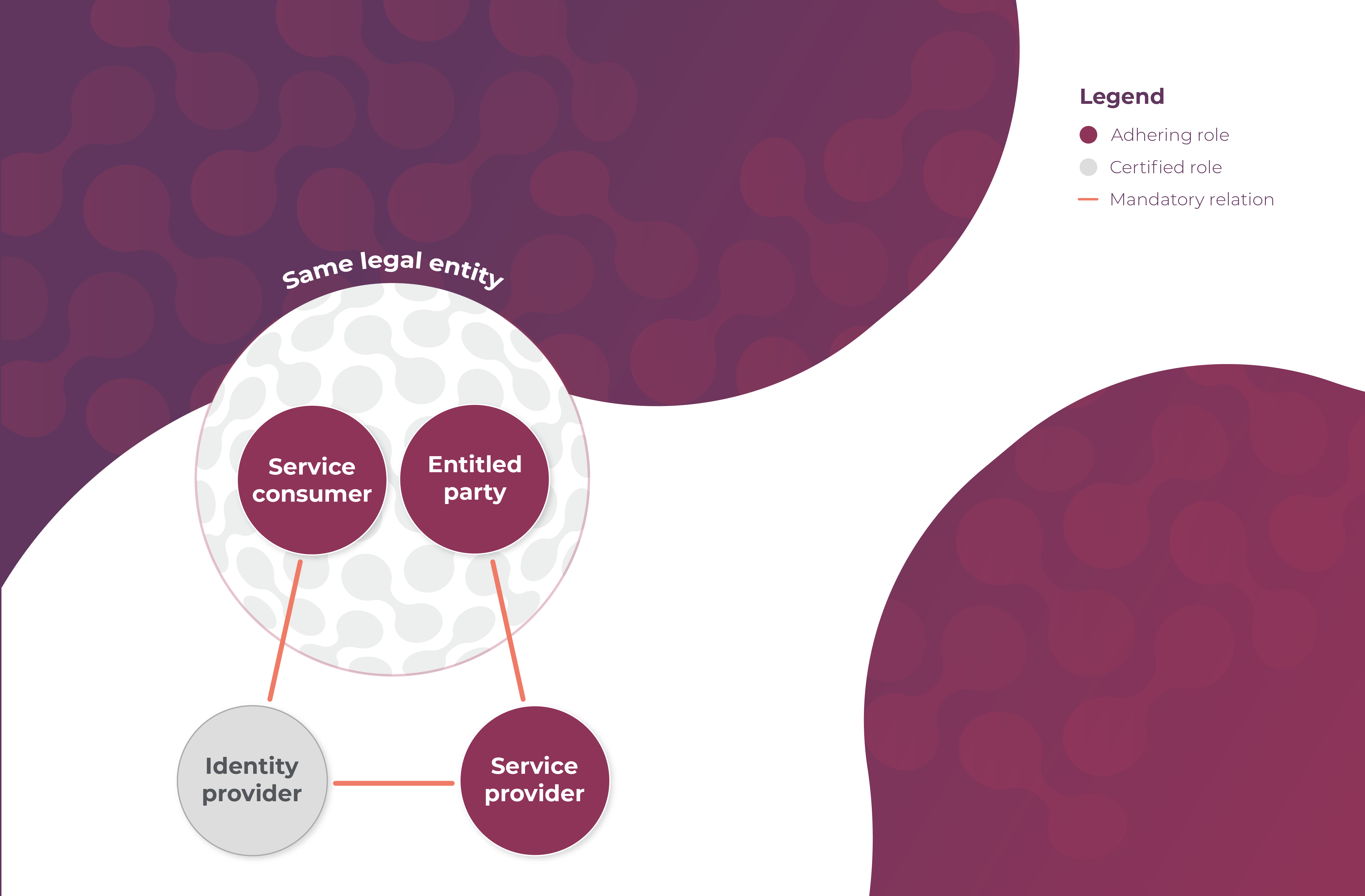
Authorisation via Participant Registry Verifying Service Consumer Before Authorisation Check